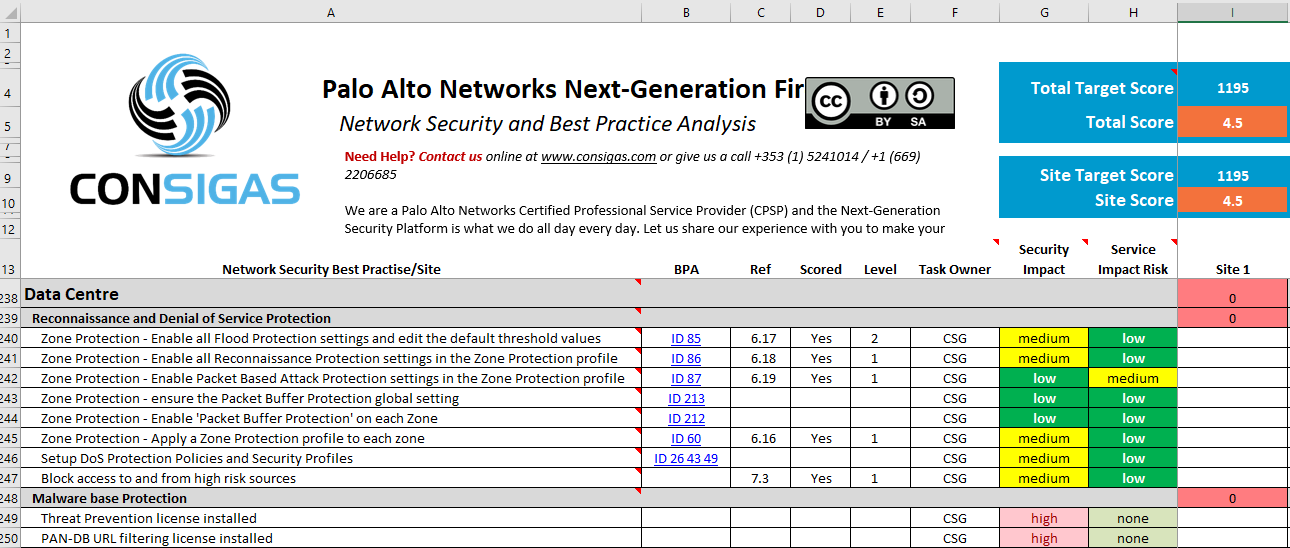
If implemented and managed correctly, the Palo Alto Networks Next-Generation FireWall is one of the few security solutions that can truly protect enterprises from modern cyber threats without negatively affecting their operation. We have put our over 10 years’ experience in working with Palo Alto Networks together and compiled this list of Best Practices to help you to secure your network by leveraging the full potential of your Palo Alto Networks Next-Generation FireWall. Besides our own, it incorporates security best practices recommended by Palo Alto Networks “BPA” as well as the Center for Internet Security “CIS Controls”.
Contact us or give us a call +353 (1) 5241014 / +1 (650) 407-1995 – We are a Palo Alto Networks Certified Professional Service Provider (CPSP) and the Next-Generation Security Platform is what we do all day every day. Let us share our experience with you to make your Next-Generation Security project a smooth experience but most importantly a peace of mind by truly securing your valuable IT assets.

security-best-practises-worksheet.xlsx
url-filtering-categories-for-web-access-policy.xlsx
Think this is useful ?
Follow us on LinkedIn

This document is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. You are free to share and adapt this document as long as you give appropriate credit to the author Lars Meyer. If you remix, transform or build upon the material, you must distribute your contributions under the same license as the original.
Disclaimer: Consigas Limited accepts no liability for the content of this blog post, or for the consequences of any actions taken on the basis of the information provided. Any views or opinions presented in this document are solely those of the author and do not necessarily represent those of Palo Alto Networks.
